How to Verify PGP Signature of Downloaded Software on Linux
PGP (Pretty Good Privacy) is a public key cryptography software that can be used to encrypt and sign data communication. In this tutorial, we will look at how to verify the PGP signature of software downloaded from the Internet on Linux.
Linux users can securely install software from their distribution’s repositories. But there are times when you need to download and install software from a website. How can you be sure that the software you downloaded wasn’t tampered with?
Some software authors sign their software using a PGP program such as GPG (GNU Privacy Guard), which is a free software implementation of the OpenPGP standard. In that case, you can verify the integrity of software using GPG.
The process is relatively simple:
- You download the public key (
.ascfile) of the software author. - Check the public key’s fingerprint to ensure that it’s the correct key.
- Import the correct public key to your GPG public keyring.
- Download the PGP signature file (
.sig) of the software. - Use public key to verify PGP signature. If the signature is correct, then the software wasn’t tampered with.
We will use VeraCrypt as an example to show you how to verify PGP signature of downloaded software.
Example: Verify PGP Signature of VeraCrypt
Although VeraCrypt is open source software, it isn’t included in Ubuntu repository. We can download VeraCrypt Linux installer from official website. I use Ubuntu 20.04 desktop, so I download the .deb file for Ubuntu 20.04.
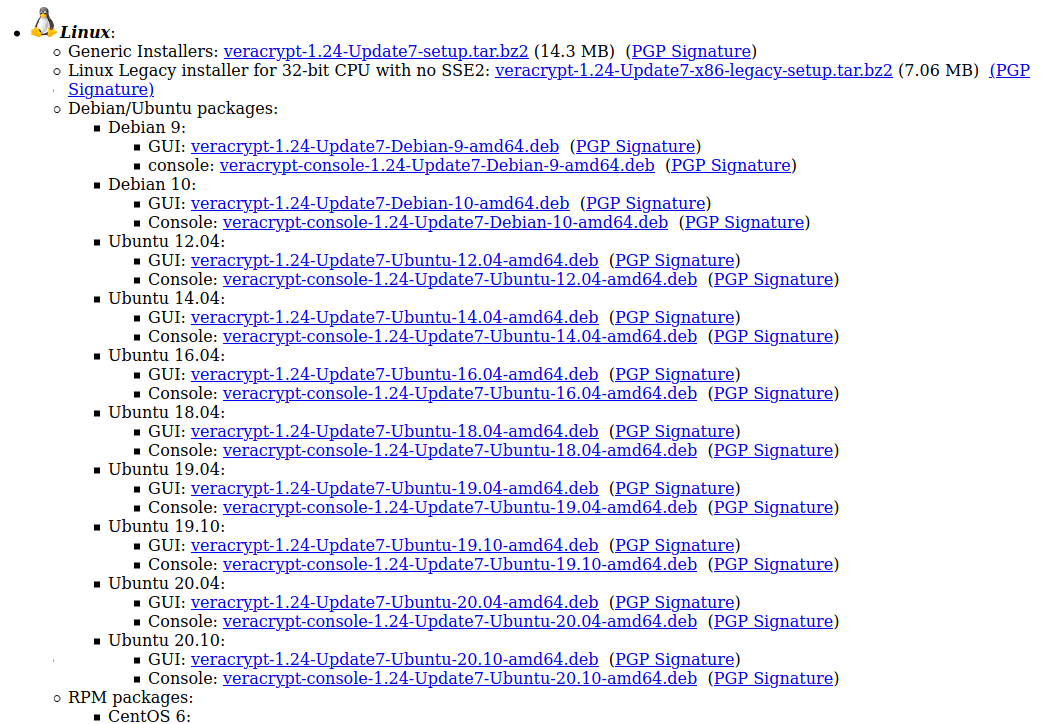
On the VeraCrypt download page, you can also find the PGP public key and PGP signature download link. Click the links to download these two files. You can run the following command to download PGP public key of VeraCrypt.
wget https://www.idrix.fr/VeraCrypt/VeraCrypt_PGP_public_key.asc
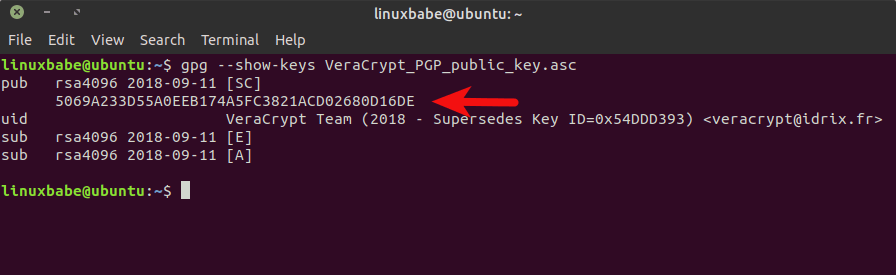
Before you do anything with the public key, you must always check the key’s fingerprint to see if it’s the correct key. Display the fingerprint of the key using the command below.
gpg --show-keys VeraCrypt_PGP_public_key.asc
The second line of the output is the key’s fingerprint.
If you are using a very old version of GPG (gpg --version) like 1.4.20, then use the following command to display the fingerprint.
gpg --with-fingerprint VeraCrypt_PGP_public_key.asc
Compare it with the fingerprint published on VeraCrypt website.
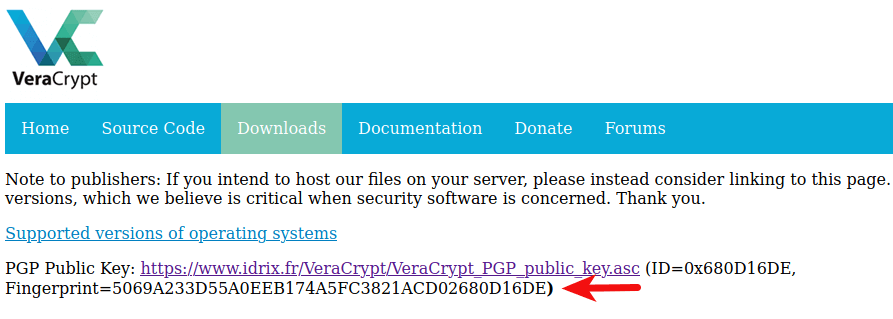
As you can see, the two fingerprints are identical, which means the public key is correct. So you can import the public key to your GPG public keyring with:
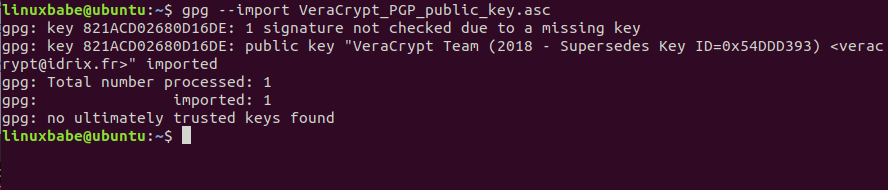
gpg --import VeraCrypt_PGP_public_key.asc
Now verify the signature of the software installer file using the command below. You need to specify the signature file (.sig) and the software installer file. This is a detached signature, meaning that the signature and software are in separate files.
gpg --verify veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb.sig veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb
The output should say “Good Signature”.
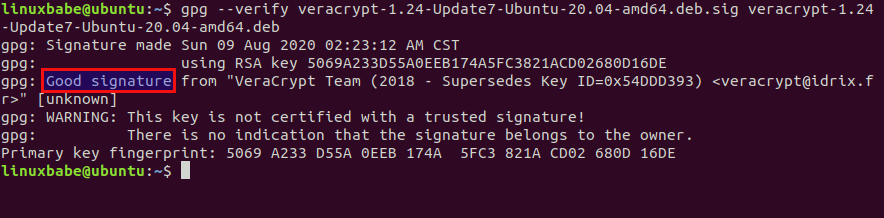
How signature verifications works:
- The signature is a hash value, encrypted with the software author’s private key.
- GPG uses the public key to decrypt hash value.
- GPG calculates the hash value of VeraCrypt installer and compare the two.
- If these two hash values match, then the signature is good and the software wasn’t tampered with.
If GPG tells you it’s a bad signature, then the software installer was tampered with or corrupted.
Importing Public Key from a Trusted Source
Note that if the software author tells you his/her public key ID on the website, then you can import the public key with the following command, so you don’t have to manually download the PGP public key and import it to your keyring.
gpg --recv-keys <key-ID>
Then display the fingerprint with:
gpg --fingerprint <key-ID>
And compare the fingerprint from output with the one published on website. This is more secure because the public key is imported from a public key server, which by default is set to hkp://keys.gnupg.net in ~/.gnupg/gpg.conf file. There’re hundreds of public keyservers around the world. Ubuntu has their own key server. MIT also has one.
If you see the following error,
gpg: keyserver receive failed: No data
then you can try a different key server, like this:
gpg --keyserver hkps://keyserver.ubuntu.com --recv-keys 0x680D16DE
That’s it!
I hope this tutorial helped you verify PGP signature of software downloads. As always, if you found this post useful, then subscribe to our free newsletter or follow us on Twitter or like our Facebook page.



Thank you and well done play by play!
Thank you!
You are welcome 🙂
Hi….
Is it not enough if we just use checksum? Why?
Thank you
I get the following error:
ubuntu@ubuntu:~$ gpg –with-fingerprint VeraCrypt_PGP_public_key.asc
I’m using Ubuntu 18.04.01 Live USB with persistence.
If you use GPG version 2.x (
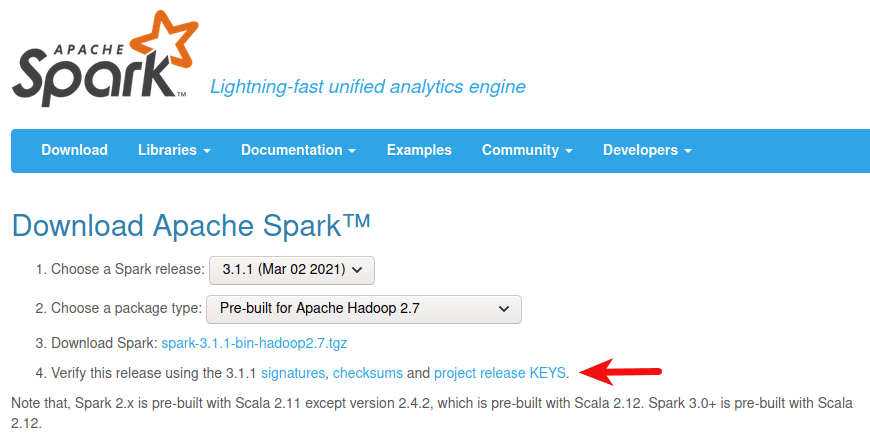
gpg --version), then use the--show-keysoption to display the fingerprint.In your tutorial, you used wget to download the detached keys for verification purposes. How did you know where to find them? I am trying to do this process for Apache Spark, but I can’t find the .asc file that the Apache Software Foundation says is supposed to be there. Thanks!
You can find the PGP public key and signature file on the software official website: https://spark.apache.org/downloads.html
This is completely different from the instructions on the Tor website at https://support.torproject.org/tbb/how-to-verify-signature/
Sometimes you can do something in multiple ways.
The overall process is the same, with some differences in the command line arguments.
Where have I gone wrong.?
rod@rod:~$ wget https://www.idrix.fr/VeraCrypt/VeraCrypt_PGP_public_key.asc --2021-05-14 14:02:12-- https://www.idrix.fr/VeraCrypt/VeraCrypt_PGP_public_key.asc Resolving www.idrix.fr (www.idrix.fr)... 51.210.181.103 Connecting to www.idrix.fr (www.idrix.fr)|51.210.181.103|:443... connected. HTTP request sent, awaiting response... 200 OK Length: 5434 (5.3K) [text/plain] Saving to: 'VeraCrypt_PGP_public_key.asc’ VeraCrypt_PGP_publi 100%[===================>] 5.31K --.-KB/s in 0s 2021-05-14 14:02:15 (97.9 MB/s) - 'VeraCrypt_PGP_public_key.asc’ saved [5434/5434] rod@rod:~$ gpg --show-keys VeraCrypt_PGP_public_key.asc pub rsa4096 2018-09-11 [SC] 5069A233D55A0EEB174A5FC3821ACD02680D16DE uid VeraCrypt Team (2018 - Supersedes Key ID=0x54DDD393) sub rsa4096 2018-09-11 [E] sub rsa4096 2018-09-11 [A] rod@rod:~$ gpg --with-fingerprint VeraCrypt_PGP_public_key.asc gpg: WARNING: no command supplied. Trying to guess what you mean ... pub rsa4096 2018-09-11 [SC] uid VeraCrypt Team (2018 - Supersedes Key ID=0x54DDD393) sub rsa4096 2018-09-11 [E] sub rsa4096 2018-09-11 [A] rod@rod:~$ gpg --import VeraCrypt_PGP_public_key.asc gpg: key 821ACD02680D16DE: 1 signature not checked due to a missing key gpg: key 821ACD02680D16DE: public key "VeraCrypt Team (2018 - Supersedes Key ID=0x54DDD393) " imported gpg: Total number processed: 1 gpg: imported: 1 gpg: no ultimately trusted keys found rod@rod:~$ gpg --verify veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb.sig veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb gpg: can't open 'veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb.sig': No such file or directory gpg: verify signatures failed: No such file or directory rod@rod:~$ gpg --verify veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb.sig veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb gpg: can't open 'veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb.sig': No such file or directory gpg: verify signatures failed: No such file or directory rod@rod:~$ gpg --import VeraCrypt_PGP_public_key.asc gpg: key 821ACD02680D16DE: 1 signature not checked due to a missing key gpg: key 821ACD02680D16DE: "VeraCrypt Team (2018 - Supersedes Key ID=0x54DDD393) " not changed gpg: Total number processed: 1 gpg: unchanged: 1 rod@rod:~$ gpg --verify veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb.sig veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb gpg: can't open 'veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb.sig': No such file or directory gpg: verify signatures failed: No such file or directory rod@rod:~$ gpg --recv-keys bash: syntax error near unexpected token `newline' rod@rod:~$ gpg --recv-keys bash: syntax error near unexpected token `newline' rod@rod:~$ gpg --fingerprint bash: syntax error near unexpected token `newline' rod@rod:~$ gpg --keyserver hkp://keyserver.ubuntu.com --recv-keys 0x680D16DE gpg: key 821ACD02680D16DE: "VeraCrypt Team (2018 - Supersedes Key ID=0x54DDD393) " not changed gpg: Total number processed: 1 gpg: unchanged: 1 rod@rod:~$ gpg --show-keys VeraCrypt_PGP_public_key.asc pub rsa4096 2018-09-11 [SC] 5069A233D55A0EEB174A5FC3821ACD02680D16DE uid VeraCrypt Team (2018 - Supersedes Key ID=0x54DDD393) sub rsa4096 2018-09-11 [E] sub rsa4096 2018-09-11 [A] rod@rod:~$Copy and paste without thinking.
You need to know
1.) your current working directory, which can be shown with
pwdcommand2.) which directory the signature file and software installer file are downloaded to.
Also use the
command to check the files in the current directory to make sure the file is there. Check to make sure the file isn’t misspelled. Usually you can copy and paste from the terminal window by doing CTRL+SHIFT+C and CTRL+SHIFT+V, so you don’t need to type manually.
hkps:
* https://en.wikipedia.org/wiki/Key_server_(cryptographic)
Ok – I am using gpg v2.2.4 under Zorin v15.3 (Ubuntu 18.04) and there is NO
shows-keysCommand, so it must be something different and in scanning the output of the Command I am at a loss to see which one it is.I reproduce here:
====================================
Commands: -s, --sign make a signature --clear-sign make a clear text signature -b, --detach-sign make a detached signature -e, --encrypt encrypt data -c, --symmetric encryption only with symmetric cipher -d, --decrypt decrypt data (default) --verify verify a signature -k, --list-keys list keys --list-signatures list keys and signatures --check-signatures list and check key signatures --fingerprint list keys and fingerprints -K, --list-secret-keys list secret keys --generate-key generate a new key pair --quick-generate-key quickly generate a new key pair --quick-add-uid quickly add a new user-id --quick-revoke-uid quickly revoke a user-id --quick-set-expire quickly set a new expiration date --full-generate-key full featured key pair generation --generate-revocation generate a revocation certificate --delete-keys remove keys from the public keyring --delete-secret-keys remove keys from the secret keyring --quick-sign-key quickly sign a key --quick-lsign-key quickly sign a key locally --sign-key sign a key --lsign-key sign a key locally --edit-key sign or edit a key --change-passphrase change a passphrase --export export keys --send-keys export keys to a keyserver --receive-keys import keys from a keyserver --search-keys search for keys on a keyserver --refresh-keys update all keys from a keyserver --import import/merge keys --card-status print the card status --edit-card change data on a card --change-pin change a card's PIN --update-trustdb update the trust database --print-md print message digests --server run in server mode --tofu-policy VALUE set the TOFU policy for a key Options: -a, --armor create ascii armored output -r, --recipient USER-ID encrypt for USER-ID -u, --local-user USER-ID use USER-ID to sign or decrypt -z N set compress level to N (0 disables) --textmode use canonical text mode -o, --output FILE write output to FILE -v, --verbose verbose -n, --dry-run do not make any changes -i, --interactive prompt before overwriting --openpgp use strict OpenPGP behavior (See the man page for a complete listing of all commands and options) Examples: -se -r Bob [file] sign and encrypt for user Bob --clear-sign [file] make a clear text signature --detach-sign [file] make a detached signature --list-keys [names] show keys --fingerprint [names] show fingerprints Please report bugs to .=============================================
?
Thanks Xiao, clearly explained. I will add that pgp key blocks can be verified by copying and pasting into the command line as well so don’t need to save to file.
I am stuck on the last step. I copy and pasted gpg –verify veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb.sig veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb.
Instead of getting the gpg: good signature I get verified signatures failed: no such file or directory.
How do I solve this?
Is anyone available to help me? I am stuck on the last step.
you probably saved both downloads from veracrypt to your downloads directory; use command cd Downloads/ and then gpg –verify veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb.sig veracrypt-1.24-Update7-Ubuntu-20.04-amd64.deb and you should be good.
Thank you for the response Pengu.
I entered cd Downloads/ into the terminal and it responded with ~/Downloads$. I then copy and pasted the command you provided above after the cs Downloads/ and it came back with WARNING: No command supplied. I also tried both the commands you provided separately and it didn’t work.
Did I enter it in wrong? It’s not letting me attach a screenshot atm so I can’t show you what I am seeing unfortunately.
I just restarted from the beginning this time making sure I saved the files into the download folder so they are all together. Still got the same response. Is there something I need to do before installing and verifying the program?
You need to know the name of your files.
Change to the Downloads directory.
Then list files under this directory.
This is a great post! I have been struggling with verifying software downloads on Linux for a while now. This is a great guide!
Hello Guoan.
I just downloaded the latest update to LibreOffice for Mac, along with a signature file in .asc format. The public key for the file downloaded is not shared on the site with the downloads. And AFAIK I am not able to verify the download without having the PGP key in my keyring.
Is it possible to ascertain what key produced the signature file, and how would I do it in MacOS or Linux?
I have done some searching and have not found an answer to my question.
Thank you.
If there is a Linux system connected with a linked account in your Google account and also not able to remove it. Is it possible that the person controlling the Linux system would be able to copy my gpg and kind of clone my signature if I’m unaware? This is the 1st time I’ve heard about gpg and veracrypt and honestly y’all trying to follow that step by step guide I’m lost. Maybe a protect your online presence beginner guide would be a great 1st step. Appreciate the yes or no on the Linux hijack question, also would appreciate a website for beginners please and thanks. No excuses on my part I’ve been asleep at the wheel, good thing it’s a metaphor/simile
Thanks friend
Hi all,
All i want is to verify sha256 and 512sum files against the sha256 or 512sums.gpg file of the iso image i downloaded. The iso is the debian 12.9 os.
Very informative tutorial. However i tried to verify with no success
I run a Xubuntu machine and i tried also to verify xubuntu 22.04 iso also with no success.
I don’ t know from where to retrieve the public key of debian and then i need also the key fingerprint. I’ m rather confused. i don’ t have a private key as i don’ t think i need it for the time being.
In plus the debian sign file is .sign and not .gpg as it is in ubuntu.
Do i have to run debian machine so to access debian keyserver ? What the workaround would be for achieving it ? Any recommendation will be very helpful
100x🙏!