Set Up SSH Two-Factor Authentication (2FA) on CentOS/RHEL Server
This tutorial will show you how to set up SSH two-factor authentication on CentOS/RHEL server using the well-known Google Authenticator. It will greatly improve the security of SSH service on your CentOS/RHEL server.
How Two-Factor Authentication Works
Usually you only need to enter a password or use SSH key to log in to your remote CentOS/RHEL server. Two-factor authentication (2FA) requires you to enter two pieces of information in order to login, so you will also need to enter a time-based one-time password to log in to your SSH server. This one-time password is computed using the TOTP algorithm, which is an IETF standard. These days many websites and services (Facebook, Google, Twitter, etc) offer 2FA for users to secure their accounts and it’s a good idea to also enable 2FA for your SSH server.
This tutorial will show you how to set up
- Password authentication with 2FA
- Public key authentication with 2FA
Note: The open-source server software we will use in this article is called google-authenticator, which is installed from the EPEL repository. Google the company does not involve in the authentication process in any shape or form. The server software and the mobile app don’t need network access.
Step 1: Install and Configure Google Authenticator on CentOS/RHEL Server
Log into your CentOS/RHEL server and run the following commands to install Google Authenticator from the EPEL (Extra Package for Enterprise Linux) repository. qrencode is used to generate QR code on the command line.
sudo dnf install -y epel-release sudo dnf install -y google-authenticator qrencode qrencode-libs
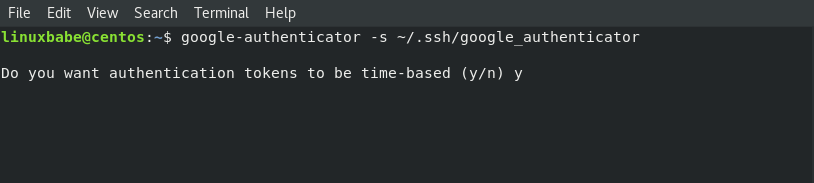
Then run the google-authenticator command to create a new secret key in the ~/.ssh/ directory.
google-authenticator -s ~/.ssh/google_authenticator
When asked “Do you want authentication tokens to be time-based?” Answer y.
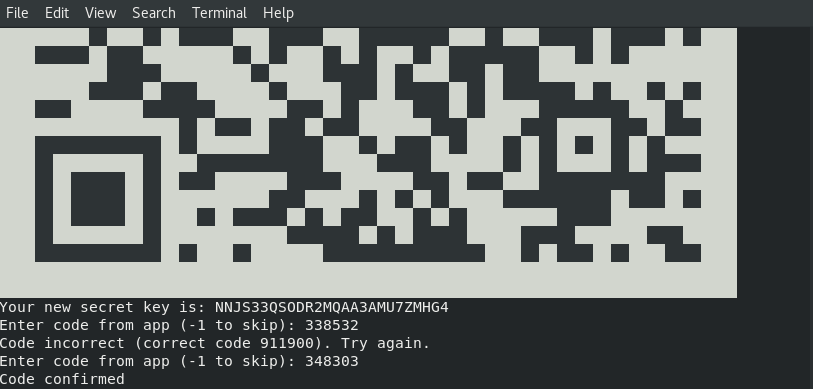
Then you will see a QR code that you need to scan using a TOTP app on your phone.
There are two apps that I recommend:
- Google Authenticator is the most well-known TOTP mobile app. You can install it via Google Play or Apple app store on your mobile phone.
- The Google Authenticator mobile app isn’t open-source. If you don’t trust Google, you can use FreeOTP, an open-source TOTP mobile app developed by Red Hat.
Scan the QR code with Google Authenticator or FreeOTP on your mobile phone. Note that you need to enlarge the terminal window to scan the full QR code.
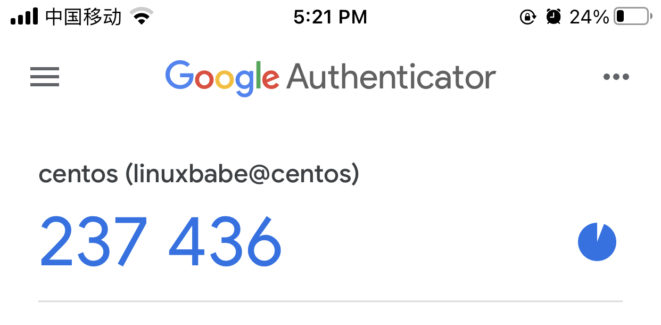
The QR code represents the secret key, which is only known by your SSH server and your TOTP mobile app. Once the QR code is scanned, you can see a six-digit one-time password on your phone. By default, it changes every 30 seconds. You need to enter this one-time password into the terminal.
Now in the terminal window, you should see the emergency scratch code. It’s important that you save this information to a safe place in case you lose your phone.
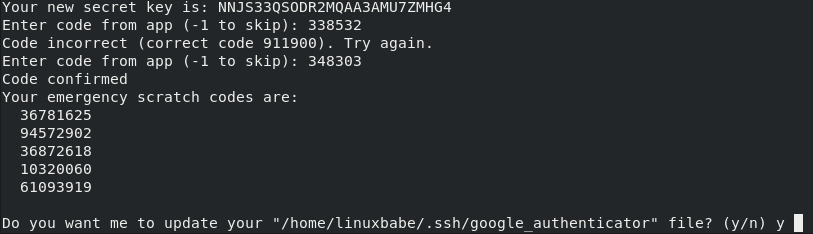
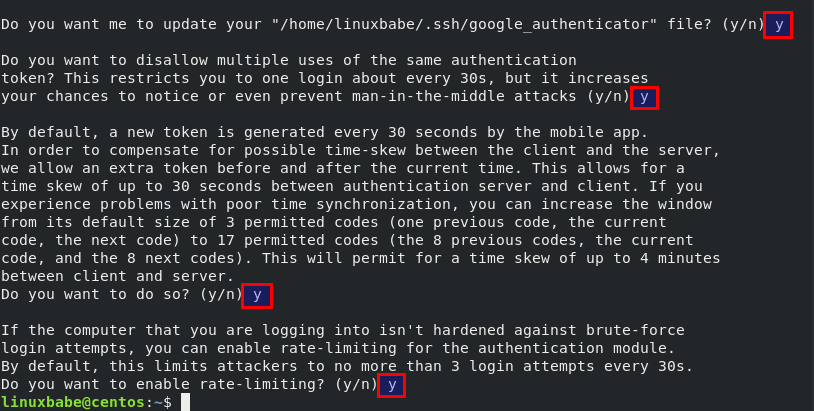
Then you can enter y to answer all of the remaining questions. This will update you Google Authenticator configuration file, disable multiple uses of the same authentication token, increase the time window and enable rate-limiting to protect against brute-force login attempts.
Step 2: Configure SSH Daemon to Use Google Authenticator
- Password authentication with 2FA
- Public key authentication with 2FA
Password Authentication with 2FA
If you don’t use SSH key, then follow the instructions below.
Open SSH server configuration file.
sudo nano /etc/ssh/sshd_config
Find the following two parameters in the file and make sure both of them are set to yes.
UsePAM yes ChallengeResponseAuthentication yes
PAM stands for pluggable authentication module. It provides an easy way to plug different authentication method into your Linux system. To enable Google Authenticator with SSH, PAM and Challenge-Response authentication must be enabled.
If you want to allow the root user to use 2FA, then find the PermitRootLogin parameter and set its value to yes. It can not be PermitRootLogin no or PermitRootLogin prohibit-password.
PermitRootLogin yes
Save and close the file. Next, edit the PAM rule file for SSH daemon.
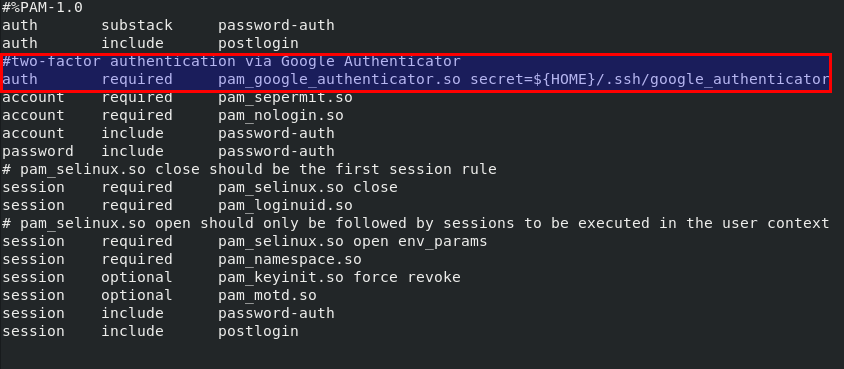
sudo nano /etc/pam.d/sshd
To enable 2FA in SSH, add the following two lines.
#two-factor authentication via Google Authenticator
auth required pam_google_authenticator.so secret=${HOME}/.ssh/google_authenticator
Save and close the file. Then restart SSH daemon for the change to take effect.
sudo systemctl restart sshd
From now on SSH daemon will require you to enter user password and a verification code (the one-time password generated by Google Authenticator). The following screenshot shows an SSH login session from an Ubuntu desktop to a CentOS Linux server.

Public Key Authentication with 2FA
If you use SSH key to log into SSH server, then follow the instructions below.
Open SSH server configuration file.
sudo nano /etc/ssh/sshd_config
Find the following two parameters in the file and make sure both of them are set to yes.
UsePAM yes ChallengeResponseAuthentication yes
PAM stands for pluggable authentication module. It provides an easy way to plug different authentication method into your Linux system. To enable Google Authenticator with SSH, PAM and Challenge-Response authentication must be enabled.
If you want to allow the root user to use 2FA, then find the PermitRootLogin parameter and set its value to yes. It can not be PermitRootLogin no or PermitRootLogin prohibit-password.
PermitRootLogin yes
Next, add the following line at the end of this file. This tells SSH daemon that the user must pass both public key authentication and challenge-response authentication.
AuthenticationMethods publickey,keyboard-interactive
Save and close the file. Next, edit the PAM rule file for SSH daemon.
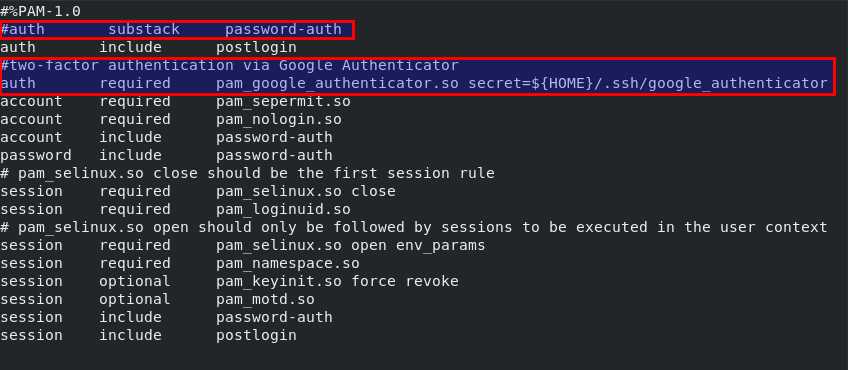
sudo nano /etc/pam.d/sshd
To enable 2FA in SSH, add the following two lines.
#two-factor authentication via Google Authenticator
auth required pam_google_authenticator.so secret=${HOME}/.ssh/google_authenticator
Also comment out the following line (Add # at the beginning) to disable password authentication.
auth substack password-auth
Save and close the file. Then restart SSH daemon for the change to take effect.
sudo systemctl restart sshd
From now on you need to use SSH key and Google Authenticator verification code to login.
Notes
- Each user on your CentOS/RHEL server needs to run
google-authenticator -s ~/.ssh/google_authenticatorcommand and scan QR code in order to use two-factor authentication. If the user didn’t set up and tries to login, the error message “Permission denied (keyboard-interactive)” will be displayed. - Emergency Scratch Code is your backup code. If you lose your phone, you can enter one of five emergency scratch code instead of a one-time password to complete the two-step verification. These codes are for one-time use only.
- If you want to change the secret key, simply log into your server and run
google-authenticator -s ~/.ssh/google_authenticatorcommand again to update the~/.ssh/google_authenticatorfile.
How to Disable SSH Two Factor Authentication on CentOS/RHEL Server
Edit the PAM rule file for SSH daemon.
sudo nano /etc/pam.d/sshd
Comment out the following line.
auth required pam_google_authenticator.so secret=${HOME}/.ssh/google_authenticator
Save and close the file. If you added the following line in /etc/ssh/sshd_config file,
AuthenticationMethods publickey,keyboard-interactive
Remove the keyboard-interactive authentication method.
AuthenticationMethods publickey
Save and close the file. Then restart SSH daemon.
sudo systemctl restart sshd
Wrapping Up
I hope this tutorial helped you set up SSH two-factor authentication on CentOS/RHEL server. As always, if you found this post useful, then subscribe to our free newsletter to get more useful tutorials. Take care 🙂



It doesn’t work with CentOS Stream 9