Install Let’s Encrypt Free TLS/SSL Certificate with Nginx on Debian 8 Server
This guide explains how to obtain and install Let’s Encrypt free TLS/SSL certificate with Nginx server on Debian 8 server.
Install Let’s Encrypt Client on Debian 8 Server
Ubuntu 16.04 repository already have Let’s Encrypt client. The client is also available in Debian testing repository. Some of you may think, “Wow, then we can enable jessie-backports repo to install Let’s Encrypt client on Debian 8!” In fact, this is what I think when I found Let’s Encrypt client is included in Debian 9 repository.
So let’s open sources.list file with nano text editor.
sudo nano /etc/apt/sources.list
then add the following line at the end of this file.
deb http://ftp.debian.org/debian jessie-backports main
And then update local package index and install letsencrypt.
sudo apt-get update sudo apt-get install letsencrypt -t jessie-backports
Obtain a Free TLS/SSL Certificate with Standalone Plugin
When we apply a TLS/SSL certificate from Let’s Encrypt with the standalone plugin, the letsencrypt client will temporarily start a Web server which listens on port 80. So if you installed Nginx Web server before and Nginx is running, then you need to stop it with the following command to release port 80.
sudo systemctl stop nginx
or
sudo service nginx stop
Then issue the following command to obtain a certificate.
sudo letsencrypt certonly --email <your-email-address> -d <your-domain-name>
The subcommmand certonly tells letsencrypt client to obtain a certificate, but do not install it because letsencrypt client doesn’t support auto-configuration for Nginx at time of writing.
Email address is used for urgent notices and lost key recovery. Replace <your-email-address> with your real email address. -d option is used to specify your domain name. Replace <your-domain-name> with your real domain name. You should point your domain name to the IP address of your Debian 8 server, otherwise domain validation will fail.
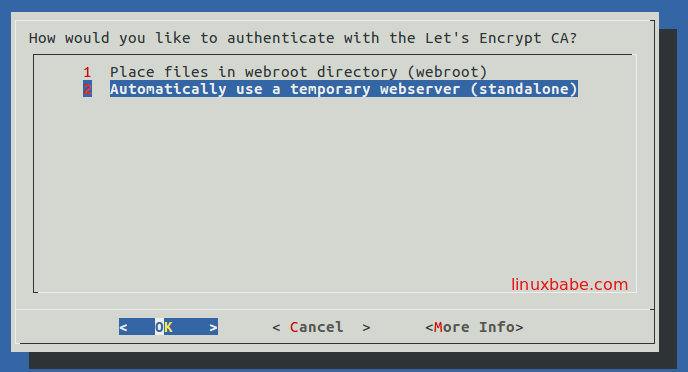
You will be asked to select the authentication method. Select the second option and hit Enter.
Within a few seconds, you should see a congrats message like below.
IMPORTANT NOTES: - Congratulations! Your certificate and chain have been saved at /etc/letsencrypt/live/your-domain-name/fullchain.pem. Your cert will expire on 2016-08-21. To obtain a new version of the certificate in the future, simply run Let's Encrypt again. - If you like Let's Encrypt, please consider supporting our work by: Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate Donating to EFF: https://eff.org/donate-le
Your certificate and chain is saved at /etc/letsencrypt/live/your-domain-name/fullchain.pem.
Install TLS/SSL Certificate with Nginx
Install Nginx with the following command if you have not already done so.
sudo apt-get install nginx
Then create server block configuration file.
sudo nano /etc/nginx/conf.d/your-domain-name.conf
Here’s a sample TLS/SSL configuration for Nginx.
server {
listen 80;
server_name www.yourdomain.com;
return 301 https://www.yourdomain.com$request_uri;
}
server {
listen 443 ssl;
server_name www.yourdomain.com;
ssl_protocols TLSv1.1 TLSv1.2;
ssl_certificate /etc/letsencrypt/live/www.yourdomain.com/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/www.yourdomain.com/privkey.pem;
access_log /var/log/nginx/www.yourdomain.com.log;
root /var/www/html;
}
Save and close the file. Restart Nginx.
sudo systemctl restart nginx
or
sudo service nginx restart
Obtain TLS/SSL Certificate with Webroot Plugin
Stopping Nginx server can lead to bad experience for your site visitors. This following steps use the Webroot plugin to obtain TLS/SSL certificate without the need to stop Nginx server.
First enter the following command.
sudo letsencrypt certonly --email <your-email-address> -d <your-domain-name>
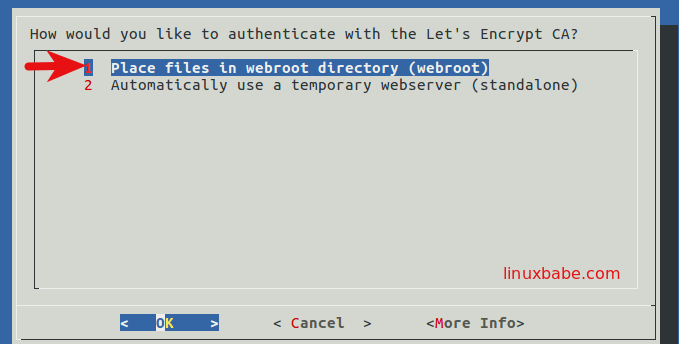
Then select the first authentication method.
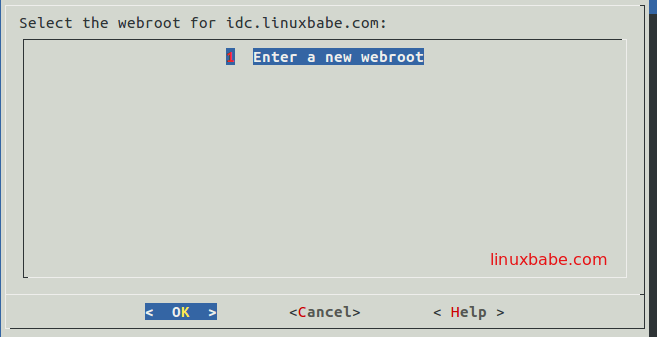
Next, hit Enter key to enter your Web root directory.
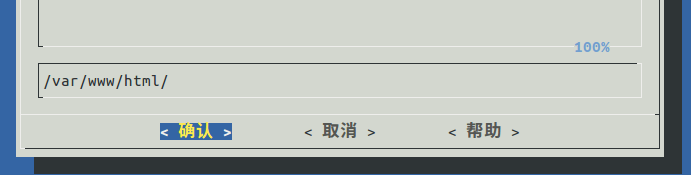
And enter your web root directory. The two common web root are /var/www/html and /usr/share/nginx/html/.
In a few seconds, your certificate will be issued by Let’s Encrypt.
The above process can be automated by adding the following option.
--webroot -w /var/www/html/
--webroot tells letsencrypt client to use Webroot plugin. -w is short for --webroot-path. /var/www/html/ is a common Web root. So you can use the following one command to obtain a TLS/SSL certificate without stopping Nginx.
sudo letsencrypt certonly --email <your-email-address> -d <your-domain-name> --webroot -w /var/www/html
You may need to add the following directives in Nginx server configuration file to allow access to .well-know directory.
location ~ /.well-known {
allow all;
}
Renew Let’s Encrypt TLS/SSL Certificate
The config directory of letsencrypt is /etc/letsencrypt under which you will find a renewal directory. Under /etc/letsencrypt/renewal are some conf files which defines how your certificate will be renewed.
Run the following command to test the renewal process on your Debian 8 server:
sudo letsencrypt renew --dry-run
You will find that letsencrypt client uses the same plugin and options that were used at the time the certificate was originally issued. This is the default behavior.
To change the plugin or options used for renewal, you have to edit the conf files under /etc/letsencrypt/renewal.
Let’s say you used the standalone plugin to obtain certificate, but now you’d like to use Webroot plugin to renew the certificate because you don’t want to stop Nginx, then open the conf file.
sudo nano /etc/letsencrypt/renewal/your-domain-name.conf
Keep the first four lines intact, change the renewal parameters to the following.
# Options used in the renewal process [renewalparams] authenticator = webroot installer = None account = 2d29325aa8757ab4198e96d1c7b46eb6 webroot_path = /var/www/html, [[webroot_map]] your-domain-name = /var/www/html
You account number can be found at /etc/letsencrypt/accounts/acme-v01.api.letsencrypt.org/directory/.
Then test renewal process again.
sudo letsencrypt renew --dry-run --webroot-path /var/www/html
You will see it’ now using the Webroot plugin to renew certificate.
To begin the real renew process, simply remove --dry-run option.
sudo letsencrypt renew --webroot-path /var/www/html
This above command will try to renew certificates that expire in less than 30 days. You can open the root user’s crontab file with the below command.
sudo crontab -e
and create a cron job.
0 5 * * * letsencrypt renew --webroot-path /var/www/html


