How to Set Up OpenLDAP Server on Debian 11
In this tutorial, we are going to take a look at installing and Configuring OpenLDAP server on Debian 11. We will also install the LDAP Account Manager web-based management tool.
What is OpenLDAP
OpenLDAP is an open-source and fast directory server that provides network clients with directory services. Client applications connect to OpenLDAP server using the Lightweight Directory Access Protocol (LDAP) to access organizational information stored on that server. Given the appropriate access, clients can search the directory, modify and manipulate records in the directory. OpenLDAP is efficient in both reading and modifying data in the directory.
OpenLDAP servers are most commonly used to provide centralized management of user accounts. For example, you can create an account in OpenLDAP and if it is connected with a mail server, FTP server, Samba server, or any other server, you can use the account to log in to these servers without creating a new account for each server.
OpenLDAP is considered lightweight in comparison to the X.500 directory service. LDAP v3 has only 9 core operations and provides a simpler model for programmers and administrators.
Step 1: Install OpenLDAP Server on Debian 11
Run the following command to install OpenLDAP server and the client command-line utilities from Debian 11 package repository. slapd stands for the Stand-Alone LDAP Daemon.
sudo apt install slapd ldap-utils
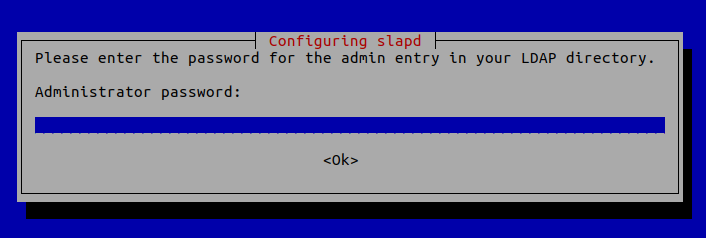
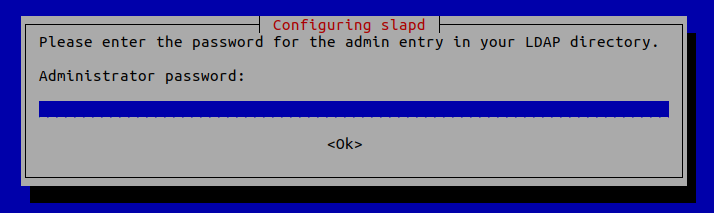
You will be asked to set a password for the admin entry in the LDAP directory.
Once it’s done, slapd will be automatically started. You can check out its status with:
systemctl status slapd
Sample output:
● slapd.service - LSB: OpenLDAP standalone server (Lightweight Directory Access Protocol) Loaded: loaded (/etc/init.d/slapd; generated) Drop-In: /usr/lib/systemd/system/slapd.service.d └─slapd-remain-after-exit.conf Active: active (running) since Wed 2022-05-25 16:28:52 CST; 13s ago Docs: man:systemd-sysv-generator(8) Process: 208178 ExecStart=/etc/init.d/slapd start (code=exited, status=0/SUCCESS) Tasks: 3 (limit: 1093) Memory: 3.1M CPU: 26ms CGroup: /system.slice/slapd.service
Hint: If the above command doesn’t quit immediately, you need to press Q to get back to the command prompt.
By default, it runs as the openldap user as is defined in /etc/default/slapd file.
Step 2: Basic Post-Installation Configuration
The installation process installs the package without any configurations. To have our OpenLDAP server running properly, we need to do some basic post-installation configuration. Run the following command to start the configuration wizard.
sudo dpkg-reconfigure slapd
You will need to answer a series of questions. Answer these questions as follows:
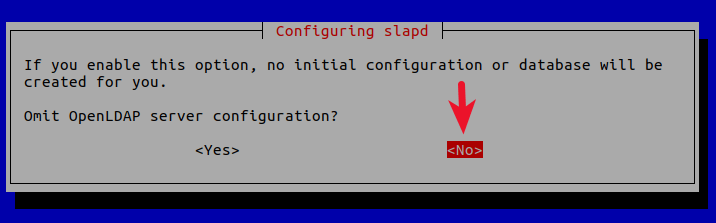
- Omit LDAP server configuration: NO.
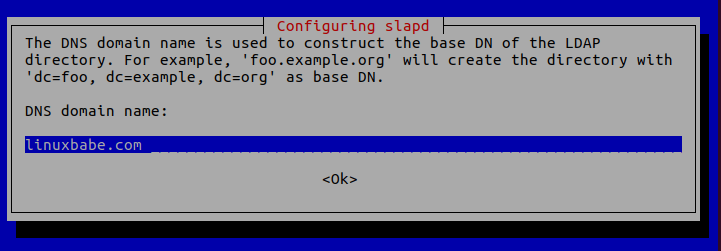
- DNS domain name: Enter your domain name like
linuxbabe.com. You will need to set a correct A record for your domain name. You can also use a subdomain likedirectory.linuxbabe.com. This information is used to create the base DN (distinguished name) of the LDAP directory.
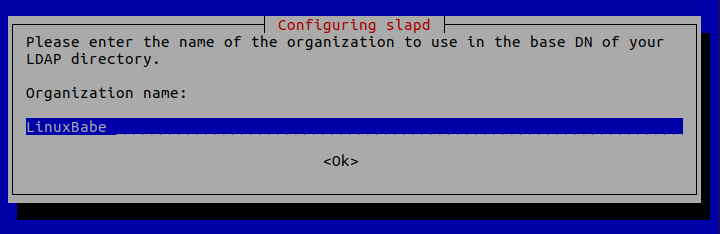
- Organization name: Enter your organization name like LinuxBabe.
- Administrator password: Enter the same password set during installation.
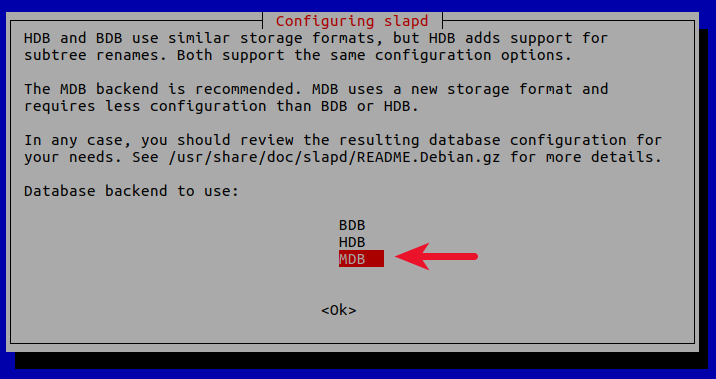
- Database backend to use: MDB.
- BDB (Berkeley Database) is slow and cumbersome. It is deprecated and support will be dropped in future OpenLDAP releases.
- HDB (Hierarchical Database) is a variant of the BDB backend and will also be deprecated.
- MDB reads are 5-20x faster than BDB. Writes are 2-5x faster. And it consumes 1/4 as much RAM as BDB. So we choose MDB as the database backend.
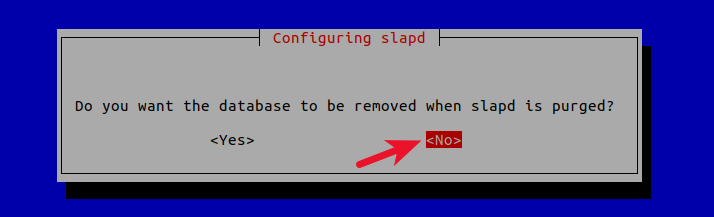
- Do you want the database to be removed when slapd is purged? No.
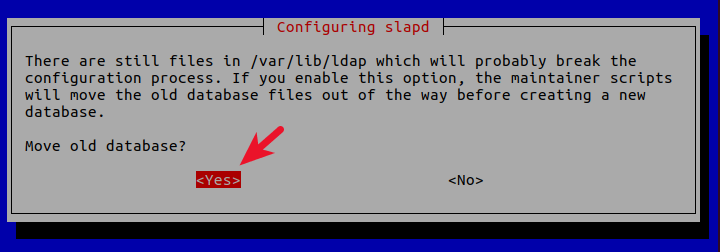
- Move old database? Yes.
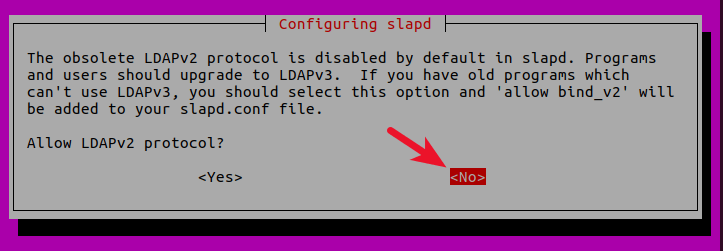
- Allow LDAPv2 protocol? No. The latest version of LDAP is LDAP v.3, developed in 1997. LDAPv2 is obsolete.
Now the process will reconfigure the OpenLDAP service according to your answers. Your OpenLDAP server is now ready to use.
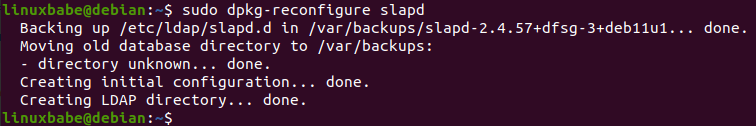
If you made a mistake, you can always run the sudo dpkg-reconfigure slapd command again to re-configure OpenLDAP.
Step 3: Configuring the LDAP Clients
/etc/ldap/ldap.conf is the configuration file for all OpenLDAP clients. Open this file.
sudo nano /etc/ldap/ldap.conf
We need to specify two parameters: the base DN and the URI of our OpenLDAP server. Copy and paste the following text at the end of the file. Replace your-domain and com as appropriate.
BASE dc=your-domain,dc=com URI ldap://localhost
The first line defines the base DN. It tells the client programs where to start their search in the directory. If you used a subdomain when configuring OpenLDAP server, then you need to add the subdomain here like so
BASE dc=subdomain,dc=your-domain,dc=com
The second line defines the URI of our OpenLDAP server. Since the LDAP server and client are on the same machine, we should set the URI to ldap://localhost. You can add multiple URIs later if the need arises.
Save and close the file.
Step 4: Testing OpenLDAP Server
Now that OpenLDAP server is running and client configuration is done, run the following command to make test connections to the server.
ldapsearch -x
Output:
# extended LDIF
#
# LDAPv3
# base <dc=linuxbabe,dc=com> (default) with scope subtree
# filter: (objectclass=*)
# requesting: ALL
#
# linuxbabe.com
dn: dc=linuxbabe,dc=com
objectClass: top
objectClass: dcObject
objectClass: organization
o: LinuxBabe
dc: linuxbabe
# admin, linuxbabe.com
dn: cn=admin,dc=linuxbabe,dc=com
objectClass: simpleSecurityObject
objectClass: organizationalRole
cn: admin
description: LDAP administrator
# search result
search: 2
result: 0 Success
# numResponses: 3
# numEntries: 2
Result: 0 Success indicates that OpenLDAP server is working. If you get the following line, then it’s not working.
result: 32 No such object
Step 5: Installing LDAP Account Manager
LDAP Account Manager is a web-based program for managing OpenLDAP server. The command-line utilities can be used to manage our OpenLDAP server, but for those who want an easy-to-use interface, you can install LDAP Account Manager.
Run the following command to install LDAP Account Manager from Debian package repository.
sudo apt install ldap-account-manager
If your Debian server doesn’t have a web server running, then the above command will install the Apache web server as a dependency. If there’s already a web server such as Nginx, then Apache won’t be installed.
Step 6: Install Required and Recommended PHP Modules
Run the following command to install PHP modules required or recommended by LDAP account manager.
sudo apt install php7.4-fpm php7.4-imap php7.4-mbstring php7.4-mysql php7.4-json php7.4-curl php7.4-zip php7.4-xml php7.4-bz2 php7.4-intl php7.4-gmp php7.4-redis
Step 7: Create a Virtual Host for LDAP Account Manager
Apache
If you use Apache web server, create a virtual host for LDAP Account Manager.
sudo nano /etc/apache2/sites-available/ldap-account-manager.conf
Put the following text into the file. Replace openldap.example.com with your real domain name and don’t forget to set DNS A record for it.
<VirtualHost *:80>
ServerName openldap.example.com
DocumentRoot /usr/share/ldap-account-manager
ErrorLog ${APACHE_LOG_DIR}/ldap-account-manager_error.log
CustomLog ${APACHE_LOG_DIR}/ldap-account-manager_access.log combined
Alias /lam /usr/share/ldap-account-manager
<Directory />
Options FollowSymLinks
AllowOverride All
Require all granted
DirectoryIndex index.html
</Directory>
<Directory /var/lib/ldap-account-manager/tmp>
Options -Indexes
</Directory>
<Directory /var/lib/ldap-account-manager/tmp/internal>
Options -Indexes
Require all denied
</Directory>
<Directory /var/lib/ldap-account-manager/sess>
Options -Indexes
Require all denied
</Directory>
<Directory /var/lib/ldap-account-manager/config>
Options -Indexes
Require all denied
</Directory>
<Directory /usr/share/ldap-account-manager/lib>
Options -Indexes
Require all denied
</Directory>
<Directory /usr/share/ldap-account-manager/help>
Options -Indexes
Require all denied
</Directory>
<Directory /usr/share/ldap-account-manager/locale>
Options -Indexes
Require all denied
</Directory>
</VirtualHost>
Save and close the file. Then enable this virtual host with:
sudo a2ensite ldap-account-manager.conf
Reload Apache for the changes to take effect.
sudo systemctl reload apache2
Now you should be able to access the LDAP Account Manager web interface at http://openldap.example.com.
Nginx
If you use Nginx web server, create a virtual host for LDAP Account Manager.
sudo nano /etc/nginx/conf.d/ldap-account-manager.conf
Copy the following text and paste it to the file. Replace ldap.your-domain.com with your preferred domain name.
server {
listen 80;
server_name openldap.your-domain.com;
root /usr/share/ldap-account-manager/;
index index.php index.html index.htm;
error_log /var/log/nginx/ldap-account-manager.error;
access_log /var/log/nginx/ldap-account-manager.access;
location ~ \.php$ {
fastcgi_pass unix:/run/php/php7.4-fpm.sock;
fastcgi_index index.php;
fastcgi_param SCRIPT_FILENAME $document_root/$fastcgi_script_name;
include fastcgi_params;
}
}
Save and close the file. Then text Nginx configurations.
sudo nginx -t
If the test is successful, reload Nginx for the changes to take effect.
sudo systemctl reload nginx
Now you can access LDAP Account Manager web interface at openldap.example.com.
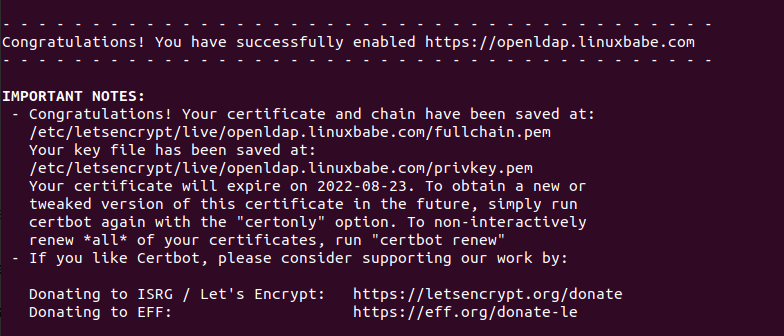
Step 8: Enabling HTTPS
To encrypt the HTTP traffic, we can enable HTTPS by installing a free TLS certificate issued from Let’s Encrypt. Run the following command to install Let’s Encrypt client (certbot) on Debian server.
sudo apt install certbot
If you use Apache, install the Certbot Apache plugin.
sudo apt install python3-certbot-apache
And run this command to obtain and install TLS certificate.
sudo certbot --apache --agree-tos --redirect --hsts --staple-ocsp --email you@example.com -d openldap.example.com
If you use Nginx, then you also need to install the Certbot Nginx plugin.
sudo apt install python3-certbot-nginx
Next, run the following command to obtain and install TLS certificate.
sudo certbot --nginx --agree-tos --redirect --hsts --staple-ocsp --email you@example.com -d openldap.example.com
Where
--nginx: Use the nginx plugin.--apache: Use the Apache plugin.--agree-tos: Agree to terms of service.--redirect: Force HTTPS by 301 redirect.--hsts: Add the Strict-Transport-Security header to every HTTP response. Forcing browser to always use TLS for the domain. Defends against SSL/TLS Stripping.--staple-ocsp: Enables OCSP Stapling. A valid OCSP response is stapled to the certificate that the server offers during TLS.
The certificate should now be obtained and automatically installed, which is indicated by the message below.
Step 9: Accessing LDAP Account Manager Web Interface
We can now test out the LDAP Account Manager tool with our web browser. When LDAP Account Manager first loads, it redirects you to the login page.
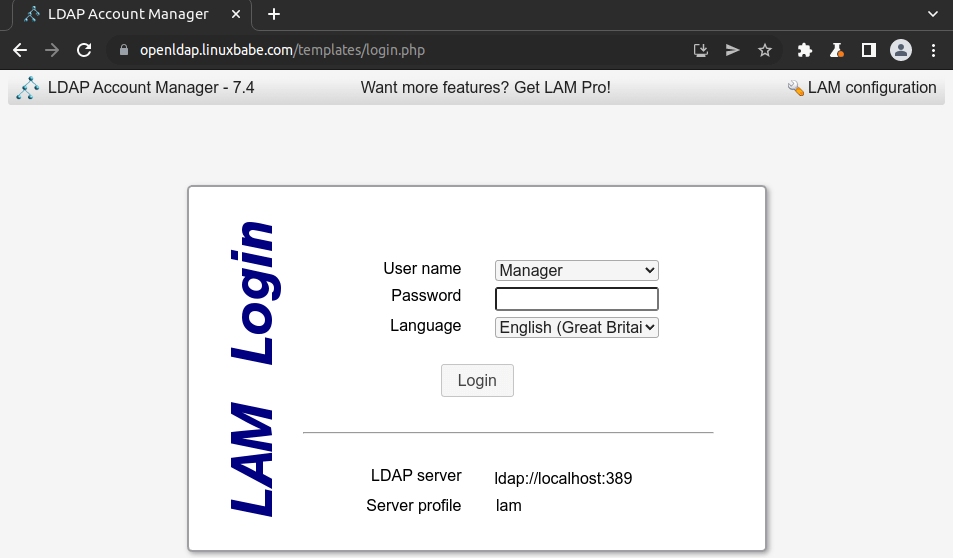
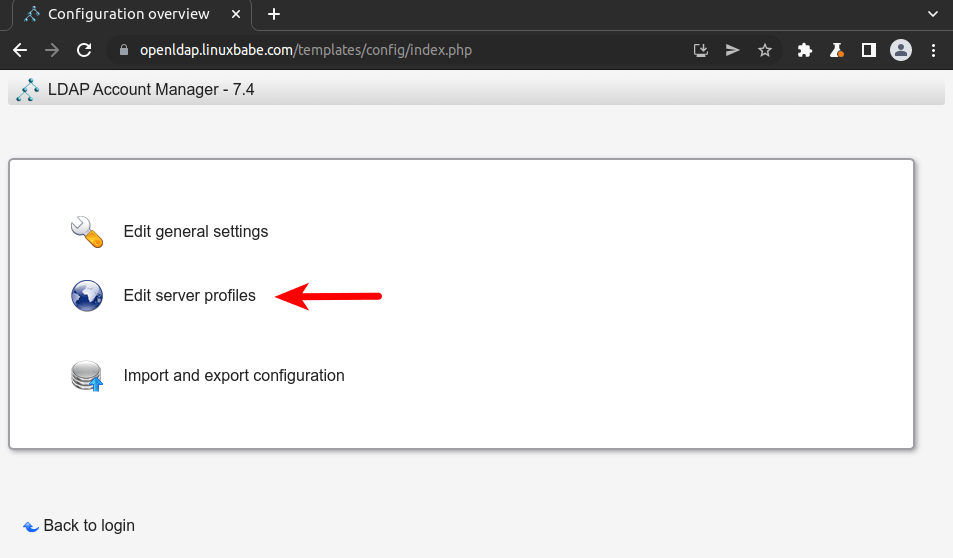
Before login, we need to configure the server profile. Click the LAM configuration link in the upper-right corner, then select Edit server profiles.
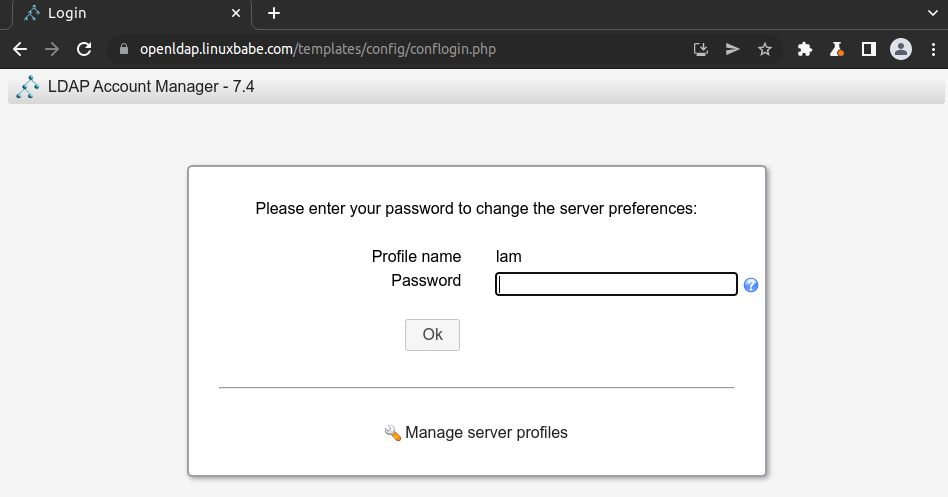
Enter the profile password, which is lam by default.
In the General settings tab, you will find the Tree suffix, which is dc=yourdomain,dc=org by default. You need to change it to your own base DN (distinguished name). In my case, I need to change it to dc=linuxbabe,dc=com.

Scroll down to the Security settings section, you will find the list of valid users. By default, there’s only one user: cn=Manager,dc=my-domain,dc=com. This is known as login DN. Change the common name (cn) to admin and also change the base DN. In my case, I need to change the login DN to cn=admin,dc=linuxbabe,dc=com.
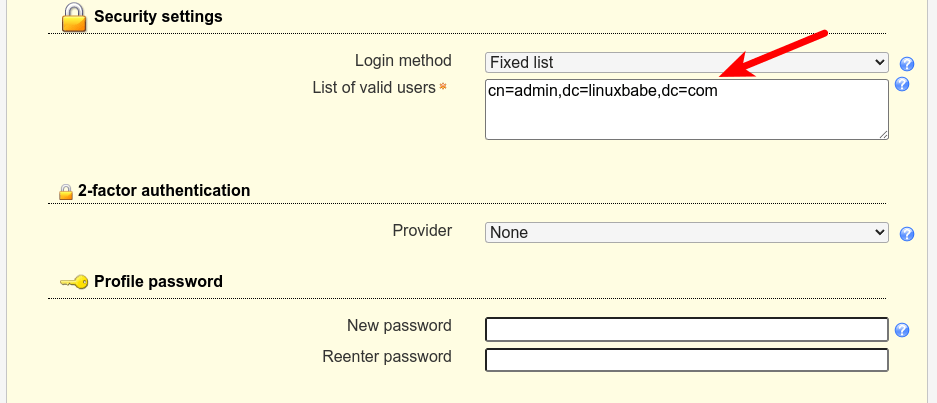
It’s also a good idea to change the default profile password.
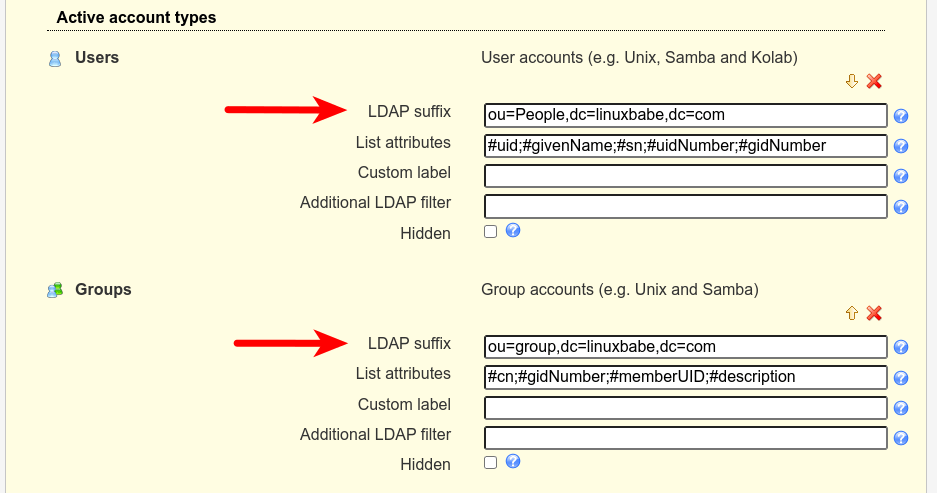
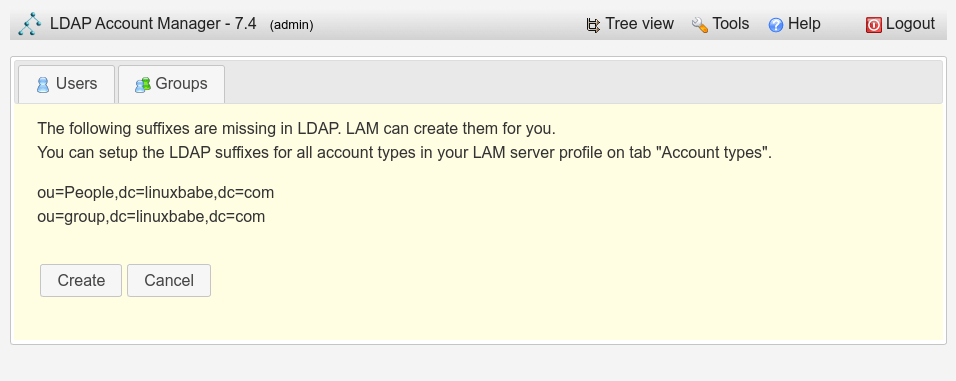
Next, scroll up and select the Account types tab. You will find the LDAP suffix for users and groups. Change them.
- ou=People,dc=linuxbabe,dc=com
- ou=group,dc=linuxbabe,dc=com
Finally, click the Save button and you will be redirected to the login page. You will be able to log in using the admin account.
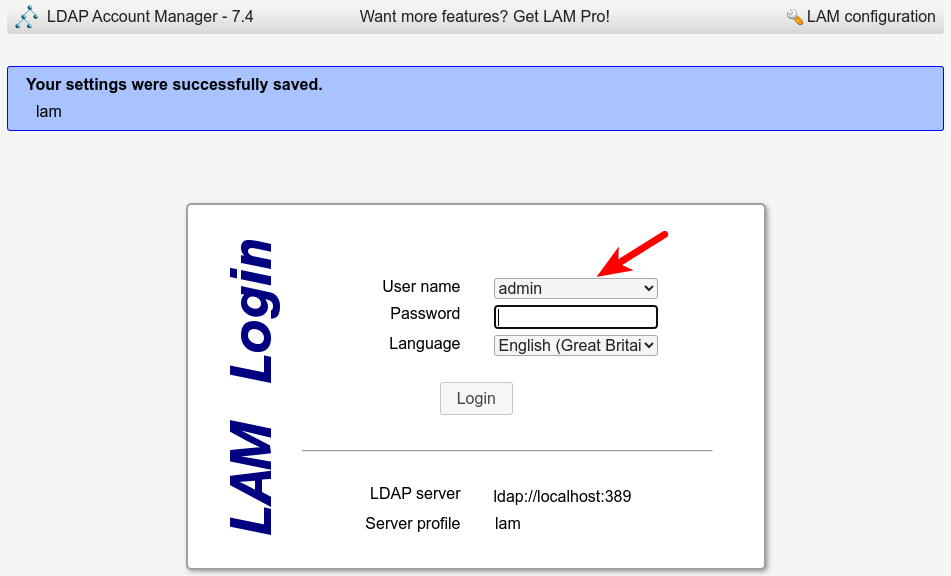
The password is the admin password you set during the configuration of OpenLDAP server in step 2. Once you log into LDAP Account Manager, you can manage this directory server.
It’s also very important to change the default master password. Log out of LDAP account manager, then select LAM configuration -> Edit General settings. Use the default master password lam to log in, then scroll down and change the master password.
Wrapping Up
That’s it! I hope this tutorial helped you install and configure both OpenLDAP server and LDAP Account Manager on Debian 11. In the next tutorial, we will see how to configure Debian to authenticate user logins with OpenLDAP.



Thanks
This is pretty good. When trying to create users, I noticed my instance complains “No Unix groups found in LDAP! Please create one first.” There are a fair number of search results that turn up using that phrasing, but none are clear or provide a solution that matches the configuration guidance given in this article. It would be tremendously helpful to provide a solution to that problem, which is LDAP Account Manager specific. I’m able to use PhpLdapAdmin to do what I need to do without issue, but I’d rather use LDAP Account Manager and I am new to it.
Thanks in advance.
how to make distribution list in phpldapadmin ? and populte that distribution list in ms outlook 2016
kindly help me
regards,